The secret history of disinformation and political warfare: Five questions for Thomas Rid
Thomas Rid is professor of strategic studies at the School of Advanced International Studies (SAIS) at Johns Hopkins University, and a grantee of the Hewlett Foundation’s Cyber Initiative. His new book Active Measures: The Secret History of Disinformation and Political Warfare has received glowing reviews on both sides of the Atlantic, including from the Washington Post’s David Ignatius, for explaining how intelligence agencies attempt to undermine their adversaries through targeted deception have evolved over the last century. We spoke to Thomas about his work at SAIS and Active Measures.
I’m curious about your career path. How would you describe your area of scholarship, and how did you arrive there?
My work is on information security and its history. I’ve always liked tinkering, secrets, and listening to good stories. And I easily get bored with a subject. So infosec[urity] is great—it’s a wide field with undefined boundaries. And so many amazing stories to tell. For example the story of NEPTUN, a 1960’s disinformation operation. Or that of the Shadow Brokers, the infamous NSA leak group. About six years ago, I discovered the joy of taking on slow-burning, in-depth investigations that take years of effort, and “all-source intelligence,” which involves working with historical archives, but also digital forensics and interviews with people involved in these stories.
How does your scholarship relate to your teaching at SAIS, and what kinds of work are you training your students to undertake?
Humboldt University in Berlin is my alma mater, and I try to apply the Humboldt philosophy: teaching and research advance and improve each other. I teach a two-term class called INFOSEC I and II. I encourage and help students to write original papers based on primary source material. One excellent essay this year, for example, was asking if the Internet Research Agency exploited mass-shooting events in the United States using various data releases to explore the question. By the time we hit the second term, my class is a veritable mini-think tank. Some of the best and most productive discussions I take part in happen in our classrooms. It’s a great privilege to teach at Johns Hopkins SAIS.
Your work related to Russia’s interference in the 2016 U.S elections has received a lot of attention, but Active Measures extends the modern history of disinformation back to the early days of the Soviet Union. How has technology changed the way intelligence services approach disinformation campaigns and what’s more enduring?
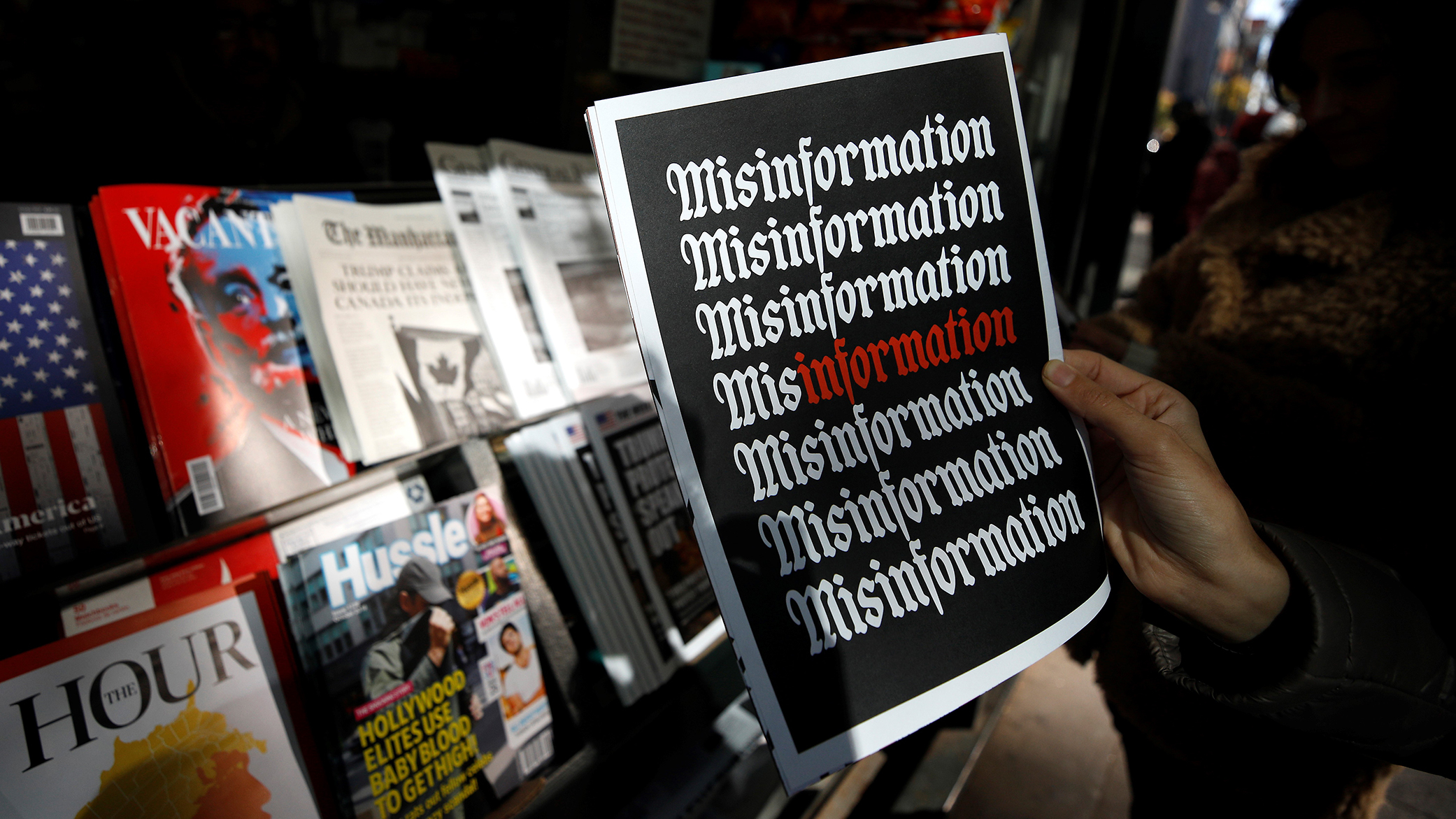
In the book, I argue that technology — and really internet culture — has made active measures more active and less measured. More active because disinformation is targeting activists of various stripes more directly—and less measured because it is even harder than it was in the past to disentangle the actual effects of a campaign from the perception of their effect. If you’re exacerbating an already existing conflict or trend, how much of it was really you’re doing? Another difference is related to data volume. Leaks and forgeries in the Cold War were often artisanal, lovingly hand-crafted because they needed to be really high-quality in order to trick professionals, mostly journalists. Today, leaks are more industrial: dumped online, in large volume, with some of the value-creation of disinformation outsourced to the victim itself, to activists and researchers and journalists who go in and report out the gems.
There’s obviously a lot of information in the new book that is difficult to obtain (whether due to government secrecy, lack of digital copies, etc.). Could you talk about how you went about researching it and your sources for it? Are there any innovative methodologies you used?
Researching Active Measures required a wide range of methods and sources: from archives of various intelligence agencies, to digital forensics, from oral history interviews, to building and maintaining relationships with private sector researchers in Digital Forensics and Incident Response (DFIR). You can see a set of the primary sources I was working from in a collection I’ve shared on Archive.org. To my own surprise, my historical research benefited from digital forensics-related work. For instance: I was able to develop a search tool that works across archival sources in different languages, which was tremendously helpful. And on the other hand, the historical case studies greatly helped me to understand the limitations — and the potential — of digital forensic artifacts in the 21st century.
Who do you see as the audience for Active Measures and what do you hope they take away from it?
The audience is really the public, but also both the infosec community as well as historians specializing in the world of intelligence. But I think the larger appeal of this book is philosophical. You can read this history on another level — where it becomes a meditation on the nature and the politics of the factual — of truth itself. Active Measures taught me something in a visceral way that I did not understand when I studied the history of science and philosophy in Berlin — that we only really appreciate the value of facts, and their fragility, when scientific objectivity is under sustained assault. An open democratic order is grounded on an open epistemic order. Facts literally keep the peace.



