For the past few months, Apple and the U.S. government have been in embroiled in an increasingly antagonistic spat about the iPhone that belonged to Syed Rizwan Farook, one of the suspects in the shooting in San Bernardino, California. The U.S. Department of Justice has sought to legally compel Apple to disable several of the phone’s security features so that the government can access its encrypted content.
The Justice Department asserts it has the authority to request assistance with this one phone in a high-profile terrorism investigation. But Apple objects to being forced to “hack” its own products. It argues that to do so would weaken the security of all iPhones, create a tool ripe for future abuse, and undermine user trust. And though the FBI requested the postponement of a key hearing in the case this week, it’s clear this fight isn’t going away. In fact, the San Bernadino iPhone case is just the latest example of how complex the debate over cybersecurity has become (For further background, see reports from two of our grantees: the Berkman Center’s Don’t Panic and MIT’s Keys Under Doormats).
Since Hewlett Foundation launched the Cyber Initiative in March 2014, cybersecurity has only become a bigger challenge. There is now wider recognition of the problem we’re focused on: Decision-makers struggling to make smart, informed cyber policy.
Stepping back and assessing our efforts to date, we saw what was working and where we could do better. Today, we’re excited to publish our “Refined Cyber Initiative Strategy.”
We have focused on field building, and that isn’t changing. Doing so allows to us to remain a neutral player —unlike government or industry — which have their own interests to look out for and often times make decisions that are short-term and reactive.
In contrast, we can play a crucial role by taking a long-term approach in service of the public interest. Our refined strategy identifies several areas where we could improve.
For example, our original goal statement was not as clear and succinct as we would like. So we updated it to describe more concretely what it is we’re trying to do: “Cultivate a field that develops thoughtful, multidisciplinary solutions to complex cyber policy challenges and catalyzes better policy outcomes.” This change in wording helps clarify that we are not focused on field building for its own sake, but rather, as the best way to generate better policy decisions.
We also decided to reformulate slightly the specific outcomes that we’re striving to achieve. They help communicate what we’re funding, what we’re not, and why. You can read the details in our report. In a nutshell, the pillars to our updated strategy are:
- Build civil society organizations that take a holistic, multidisciplinary approach to cybersecurity and contribute to a more informed policy debate
- Expand the knowledge base of existing decision-makers, and educate and empower an emerging generation of cyber policy experts
- Foster the emergence of a network—comprised of experts from industry, government, think tanks, academia, and elsewhere—that builds trust and promotes collaboration
- Fund new policy driven research and thought leadership by experts from diverse professional, political, and intellectual perspectives
- Catalyze additional funding on cyber policy topics from philanthropic, government, and private sector sources
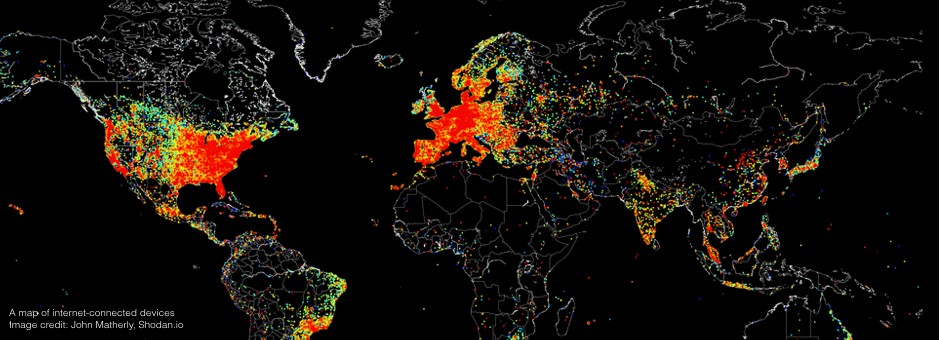
Moving forward, we will expand our grant-making to non-U.S. based grantees. It’s important to clearly embrace the global nature of cyber policy by making grants overseas. We’ve learned that U.S. grantees—even those with a fundamentally international outlook—sometimes lack credibility overseas. We plan to partner our U.S. grantees with foreign grantees to increase their effectiveness and leverage our funding for maximum impact.
Lastly, it’s worth reiterating that our funding alone will not be enough to solve the problem we’re focused on. On the contrary, the number of important funding opportunities far outstrips the funds we have available. Given the increasing challenges of cybersecurity facing the global community, we need all hands on deck, so to speak. We remain agnostic as to specific policy outcomes. Our goal is to serve a catalyst, encouraging other funders to support this vital work by showing what is possible.